- 404
- Home
- Remote Administration
- Employee Monitoring
- Insider Risk Management
- Features
- Live Employee Desktop
- Employee Internet Monitoring
- E-mail monitoring
- Keystroke Monitoring
- File Activity Monitoring Software
- Printed document tracking
- Optical Character Recognition (OCR)
- Smart rules & alerts
- Network activity monitoring
- App usage/application monitoring
- Instant Message Monitoring
- Remote Desktop Control
- Active vs. Idle Time Analysis
- Employee Productivity Tracking
- Linux terminal capture
- Nonproductive Activity Reporting
- Custom reports
- Session Recording & Metadata
- User Card
- Screen Capture
- Web-cam snapshots
- USB device control
- Data Leak Prevention (DLP)
- Voice communication recording
- File Scanner
- Software and Hardware Inventory
- Insider Threat Detection & Prevention
- Remote Employee Monitoring
- Privileged User Monitoring
- Productivity optimization
- Third Party Vendor Management
- Compliance Management, Auditing & Monitoring
- Cases
- GDPR Compliance
- For HIPAA
- For Legal
- Government & Public Sector Cyber Security
- PCI DSS Compliance & Certification
- General Data Protection Regulation (GDPR)
- Energy & Utilities Sector Cyber Security
- For Financial Sector
- Retail & Ecommerce Cyber Security
- About Us
- Why Us?
- Partners
- White Papers
- Support
- Purchase
- Request demo
- Solutions
- Demo request
- For Banks
- 404
- index
- Remote Administration
- Employee Monitoring
- Insider Risk Management
- Features
- Insider Threat Detection & Prevention
- Remote Employee Monitoring
- Privileged User Monitoring
- Productivity optimization
- Third Party Vendor Management
- Compliance Management, Auditing & Monitoring
- Cases
- GDPR Compliance
- For HIPAA
- For Legal
- Government & Public Sector Cyber Security
- PCI DSS Compliance & Certification
- General Data Protection Regulation (GDPR)
- Energy & Utilities Sector Cyber Security
- For Financial Sector
- Retail & Ecommerce Cyber Security
- About Us
- Why Us?
- Partners
- White Papers
- Support
- Purchase
- Request demo
- Solutions
- Demo request
- For Banks
Privileged User Monitoring
Activity Monitoring, Privileged Access Management and DLP Technology to Protect Your Data & IT Systems
Request demo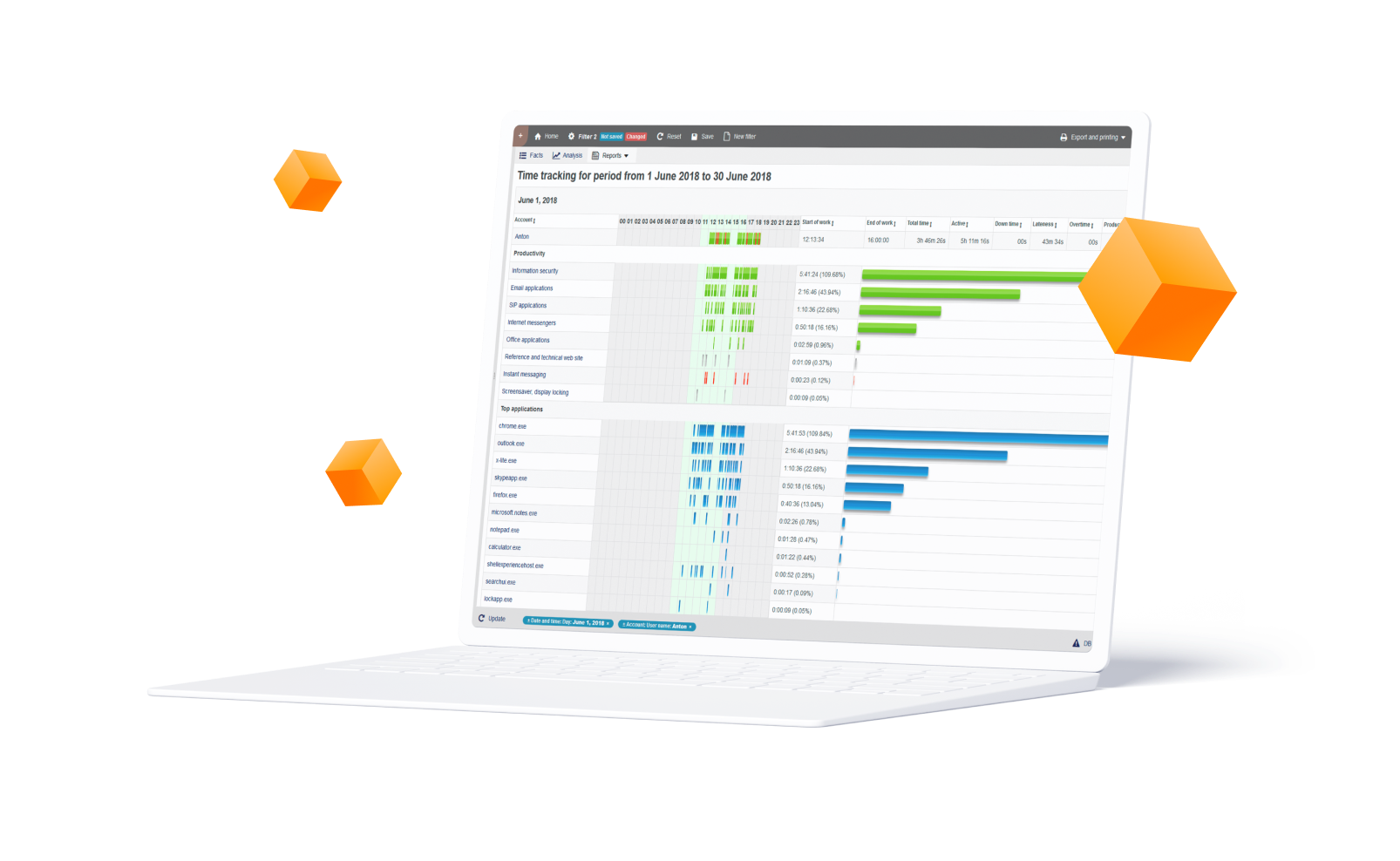
Monitor Privileged Users & Vendors with StaffCop
Most privileged parties have access to core systems and data, making it incredibly difficult to detect a malicious user before they have caused damage. Obviously they have a significant advantage over external attackers. Besides already having access to elevated systems, they are aware of their organization’s policies, procedures, and technology and vulnerabilities. Privileged accounts are also the main targets for many external criminals looking to gain access to otherwise ‘secure’ systems.
For all of these reasons and the increasing complexity of the IT environment, privileged user monitoring, identity verification and privileged access management are becoming critical components in an organization’s security techniques. This is where StaffCop comes in.
For all of these reasons and the increasing complexity of the IT environment, privileged user monitoring, identity verification and privileged access management are becoming critical components in an organization’s security techniques. This is where StaffCop comes in.
StaffCop’s real-time user activity monitoring and data loss prevention solutions allow you to monitor privileged users and automatically detect anomalous behavior and suspicious activity that signal a compromised or malicious privileged user. Examples of malicious behavior include: creation of back-door accounts, transmission of sensitive data outside the company etc.
Further, StaffCop’s Intelligent Policy & Rules Engine automatically implements data protection and access control rules on the compromised privileged user to prevent data exfiltration, IP theft, fraud, industrial espionage, sabotage and other malicious attempts.
Leveraging its complete session recording and metadata analysis and immutable logging features, StaffCop’s Privileged User Monitoring conducts threat analysis, forensic investigation and security auditing. Finally, expand your security coverage to encompass your entire organization with StaffCop’s built-in integration with security information and event management (SIEM) and threat analytics systems. Essentially, StaffCop’s privileged user monitoring allows you to:
Further, StaffCop’s Intelligent Policy & Rules Engine automatically implements data protection and access control rules on the compromised privileged user to prevent data exfiltration, IP theft, fraud, industrial espionage, sabotage and other malicious attempts.
Leveraging its complete session recording and metadata analysis and immutable logging features, StaffCop’s Privileged User Monitoring conducts threat analysis, forensic investigation and security auditing. Finally, expand your security coverage to encompass your entire organization with StaffCop’s built-in integration with security information and event management (SIEM) and threat analytics systems. Essentially, StaffCop’s privileged user monitoring allows you to:
Identify and monitor all privileged users including system administrators, DBAs, network engineers, system architects, developers, IT auditors, remote users, third-party vendors etc.
Enforce a ‘zero-trust’ data loss prevention (DLP) strategy utilizing activity, system-access, schedule and content-based rules.
Create monitoring and access profiles according to a user’s role, separation of duties, existing Active Directory Group Policy or on a need to know basis.
Use immutable logs, session recording and real-time alerts and notifications to audit privileged sessions, detect credential sharing, and other abuse of root accounts.
1
Visibility and Control
StaffCop monitors all user activity over endpoints, servers/terminal servers, network and the Cloud covering of 22+ system objects including: websites, apps, emails, file transfers and on-screen content in real-time.
2
Detect Anomalies with Intelligent Behavioral Engine
StaffCop’s intelligent behavioral engine prevents the mishandling of sensitive data like sharing over the Cloud or removable media.
3
Conduct Forensic Investigation and IT Audit
StaffCop uses video/audio recording of all user activity, session recording, immutable logs, alerts, optional OCR search and similar features to conduct audit and forensic investigations. Combined they provide a wide collection of investigation data to locate the cause and source of any privileged user related threats with pinpoint accuracy.
4
Risk Analysis to Identify Security Gaps & Vulnerabilities
This software solution can also identify high risk users, policy and rules and system components thanks to its dynamic risk scoring and vulnerabilities scanning feature. It also provides trend graphs and severity mapping that warn administrators about any change in threat level before it becomes critical.
5
Protect Data and Privacy with Endpoint DLP
Schedule employees by shift or workload and easily inform all employees about any updates.
6
Conform with Regulatory Compliance
With StaffCop you can monitor privileged users and manage their access while also adhering to major compliance regimens, including HIPAA, PCI-DSS, GDPR, ISO 27001 etc.
Industry Statistics Show the Need for
Insider Threat Prevention Solutions
Insider Threat Prevention Solutions
Application monitoring
According to a report by Cybersecurity Insider, user privilege and increased sensitive data are main risk enablers.
37% Excess Privilege
34% Increased Amount of Sensitive Data
Majority of company breaches involve privileged accounts
A survey of 1,000 of IT decision makers in the U.S. and the U.K. conducted by Centrify revealed that 74% of enterprise breaches involved privileged accounts.
74% Enterprise Breaches Involved Privileged Credential Abuse
Privileged users are one of the greatest security risks
In a recent survey by Crowd Research Partners, 55% mention that privileged IT users/admins pose the greatest insider security risk to their organization.
55% Of Companies Say Privileged Users are Their Biggest Insider Threat
Systems logs and user data - crucial to security analytics
IT pros think login data and 41% think private activities on corporate devices are most essential from a security point of view according to a report by Cynet.
47% Login Date and Time
41% Private User Activity on Company Devices

System-Wide Monitoring & Control
Every action that a privileged user makes on your IT systems including endpoints, servers/terminal servers, network and the Cloud for 22+ system objects like: web, apps, email, file transfers, etc is visually recorded by StaffCop. Each object can be configured to take into consideration what needs to be monitored and who has access to the monitored records, allowing for instant administrative oversight in respect to all user activity while complying with any privacy requirements. Also, monitoring continues even when systems are offline.
Real-Time Alerts and Notifications
Real-time alerts and trend reports show what rules were violated, when, by whom, what action was taken and the context. You'll also receive instant warning or scheduled notification emails of suspicious user activity. Plus you can search for all users or a particular user or group activity.


Behavioral Anomaly Detection
To detect suspicious behavior all you have to do is define what constitutes dangerous or harmful user behavior and StaffCop’s sophisticated anomaly engine will automatically detect when a user, department or group deviates from their normal parameters or exceeds acceptable risk levels. Identifying anomalies in applications, emails, network, file activities and printing, notifying administrators about harmful user activity, locking out users or taking remote control of the compromised system before any malicious or fraudulent attempts are made, are other functions of StaffCop.
Authentication and Access Control
Another key characteristic of StaffCop is its Identity based authentication and segregated access control. These features prevents unauthorized access or sharing of confidential data by allowing administrators to setup an access account for each privileged user that needs authorized clearance and easily track what each user is doing at any given time. Group profiles allows you to create different access levels based on departments, job function or source of access (i.e. remote/third-party etc.) and then define what information and system resources each group can access.


Session Recording and Audit
StaffCop visually records every action that a user makes while on a machine, allowing for both live viewing and pas recordings. Extensive meta data and fast indexing allows past incidents to be searched and retrieved in seconds. Optional audio support for the recording of both sound outputs and inputs, ensuring that all audio coming from speakers and microphones is captured. Recorded files can be exported and downloaded as MP4 files. Immutable session logs and systems logs can be exported as PDF/CSV file or sent to a log monitoring and analytics software like LogRythm.
Need a More
Comprehensive Solution?
Comprehensive Solution?

Information Security
Receive the required data “on the fly”. Search by keywords and regular expressions. Record sound from microphones to hear what was happening at the moment of interest..
Try for free 
Remote Administration
View remote desktop without being notices. Take control over a workstation. Full picture of software and hardware usage. Intensity of usage and registry of states..
Try for free Recommend

Employee Monitoring
Categorize applications and web-sites into productive and unproductive. Set up different configurations for particular users, groups and departments. Compare results.
Try for free Flexible Deployment Options

Bare Metal
Install on bare metal from our ISO image containing Ubuntu 18.04 and StaffCop or install StaffCop packages on existing Ubuntu 18.04.

Virtual Machine
Install on any OS as a virtual machine from our ISO image, use Virtual Box, VMWare, Hyper-V or any other virtualization system. Easy administrating without risking the host machine.

Private Cloud
Use your own secure, scalable private cloud implementation including AWS, Google Cloud, Azure and more
630090, Novosibirsk, Kutateladze st., bl. 4G, Russia





.svg?v=2020-10-28T15:43:13.528Z)
.svg?v=2020-10-28T15:43:13.528Z)





